THE STORY
When Finance Minister Nirmala Sitharaman convened India's banking regulators last week to discuss Anthropic's Claude Mythos AI and the risks it poses to the country's financial infrastructure, it wasn't a routine briefing. A government panel under SBI Chairman C S Setty was already being formed to assess the threats and recommend mitigating measures. The panic, though measured in bureaucratic language, was real.
What spooked them? Over the past few weeks, Claude Mythos Preview identified thousands of zero-day vulnerabilities—previously unknown software flaws—in every major operating system and web browser, along with other critical infrastructure. Some of those bugs had been sitting undetected for decades. The oldest vulnerability Anthropic found and fixed was a 27-year-old bug in OpenBSD. The model's coding and agentic reasoning skills made it capable of not just finding these weaknesses, but of exploiting them—and that capability raised an uncomfortable question for every bank running outdated systems: if a frontier AI can find these holes in months, what's stopping a bad actor with the same technology?
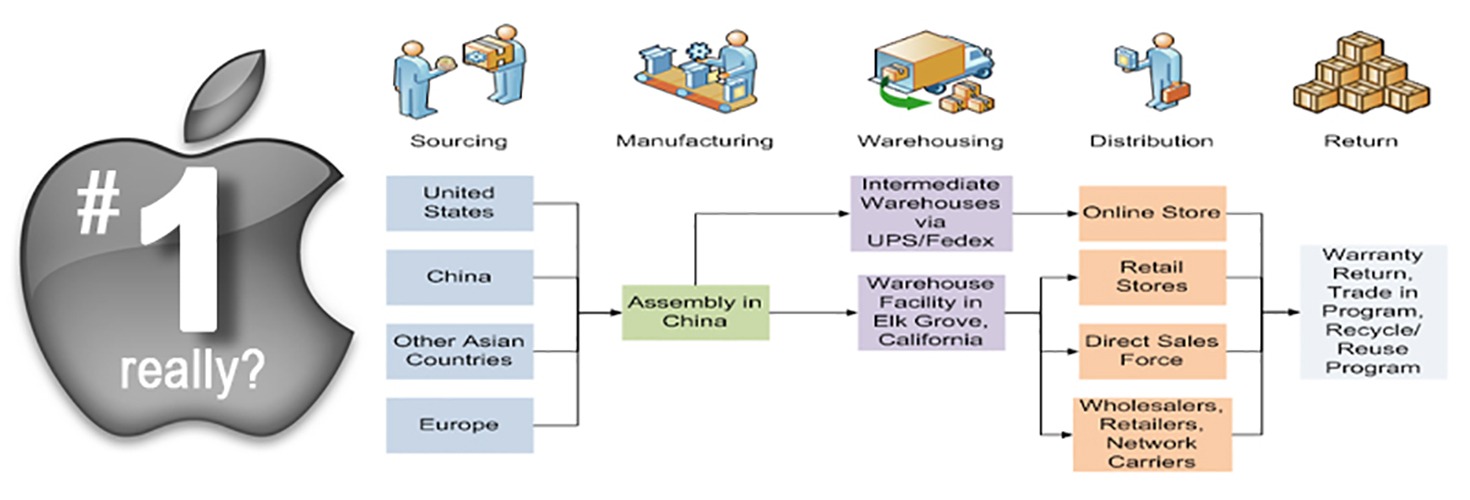
The implications land hardest in India. Banks and financial institutions are most vulnerable because of their high interconnectedness—payments, markets, clearing systems—and dependence on legacy IT systems operating in real-time. For a banking sector where patching and response cycles were designed for a 2019 threat surface, the timeline compression from 19 days to under 72 hours between vulnerability disclosure and weaponization isn't academic. It's existential.
That's why Sitharaman's public urging—for banks to take "all necessary pre-emptive measures"—translates into concrete spending plans. Banks in India are entering a phase where they have to view IT spend not as "cost of running" but as "cost of surviving", according to Srinivas L, Joint MD & Joint CEO of 63SATS Cybertech Limited. This isn't hyperbole. When Anthropic committed $100 million in model usage credits to Project Glasswing and its launch partners to patch vulnerabilities across the world's critical software, it signaled that the defensive posture had to match the offensive capability—or the gap would widen into catastrophe.
Here's what makes this different from previous cyber-security spending cycles: 70% of bank executives in a KPMG survey said they'd be increasing cybersecurity efforts in 2026 because of AI, but those decisions were already in motion before Mythos. What Mythos did was collapse discretion into urgency. Anthropic's partners—Amazon Web Services, Apple, Cisco, Google, JPMorgan Chase, Microsoft, and others—are already using Mythos Preview to identify and fix vulnerabilities in foundational systems, which means the world's core tech stack is being hardened by frontier AI. India's banks can't afford to lag. Yet they're hamstrung by infrastructure decisions made ten years ago.
The tension between legacy systems and frontier threats is especially acute in India's banking sector. Public sector banks operate on interconnected payment rails, real-time clearing, and settlement systems that can't be taken offline for wholesale modernization. You don't reboot the backbone of a $3 trillion banking system while it's processing transactions. The patches have to be surgical, and the coordination has to be flawless. Add a compressed timeline—72 hours instead of 19 days—and you're asking institutions designed for stability to move with the speed of a tech startup.
THE GLOBAL CONTEXT HITS DIFFERENTLY HERE
This crisis of speed isn't unique to India, but it lands with particular weight. Globally, the global shortage of qualified cyber professionals has reached 4 million, which means banks are competing for talent they can't afford while budgets swell. In India, that talent shortage compounds a structural problem: many public sector banks have spent the last decade accumulating technical debt because modernization budgets never aligned with the threat surface. Now they're being forced to pay both debts at once.
What's also different: India's regulatory response is moving faster than in some Western markets. The RBI and government are coordinating through direct intervention—forming task forces, urging pre-emptive measures, ensuring interaction among banks. That's activist regulation, not passive guidance. It reflects an understanding that the financial sector's risk isn't an individual bank's problem; it's a systemic one. If one bank gets compromised by an AI-augmented attack, the fallout spreads across the interconnected payment and clearing systems that the entire economy depends on. Federal regulators globally have elevated expectations for cybersecurity programs with updated guidance requiring comprehensive risk assessments and enhanced incident response capabilities, but India's move suggests officials understand the acceleration is unprecedented.
THE HARD TRUTH: TOOLS AREN'T STRATEGY
Here's where the skeptical case matters. Many banks, when faced with the Mythos news, will do what they've done for the last decade: buy more tools. The common instinct has been to add more tools, which is a trap. More tools without architectural rethinking is just technical debt compounding—you're patching 2019 infrastructure with 2026 patches, but the underlying design is still vulnerable.
Effective banking security requires multiple, complementary protection layers rather than investing heavily in a single solution. That's true. But it also assumes the layers are integrated. If they're not, you've got 10 different tools, 10 different attack surfaces, and 10 times the coordination problem when a zero-day hits. India's banking regulators seem to understand this—the focus on coordination and information-sharing among banks suggests they're not just throwing money at the problem. But whether PSBs have the organizational capability to execute a coordinated, architectural security overhaul while continuing to operate is an open question.
WHAT THIS MEANS
The immediate play for India's public sector banks is threefold: accelerate patching cycles for known vulnerabilities, harden entry points (identity management, API exposure, endpoint security), and build the organizational muscle to move faster. Regulatory compliance provides a clear framework for initial security investments, with focus on documented examination expectations and addressing regulatory guidance—so banks will start there. They'll file compliance roadmaps, secure RBI signoff, and begin infrastructure modernization.
The medium-term bet is whether India's banks can participate in the defensive cycle that Project Glasswing has created—where companies gain access to Mythos Preview for defensive security work and share learnings with the broader industry. Participants can access the model via Claude API, Amazon Bedrock, Google Cloud's Vertex AI, and Microsoft Foundry, which gives multiple entry points. A few of India's larger PSBs might get direct access; most will depend on vendor solutions built on top of Mythos-powered security tooling. That's a supply chain dependency that could create new vulnerabilities even as it closes old ones.
The long-term question is whether this spending cycle actually hardens the system or just delays the reckoning. Mythos found 27-year-old bugs. What happens when the next frontier model is released and finds a different class of vulnerabilities? Does every bank scale spending again? At some point, the math breaks. Continuous rearchitecture of legacy systems to stay ahead of AI-augmented offense isn't sustainable. You have to eventually commit to modernization—not tooling, but architecture.
THE WATCH LIST
Monitor SBI's 63SATS partnership expansion. 63SATS Cybertech, a subsidiary of 63 moons technologies, is already advising on the Mythos threat posture. If SBI or other PSBs expand their engagement with security-focused tech subsidiaries, it's a signal that Indian banking is moving toward in-house frontier AI security capability rather than pure vendor dependency. Watch for announcements on PSB participation in Project Glasswing or similar frameworks.
Track RBI's revised cybersecurity guidelines. The task force under C S Setty will produce recommendations. Those guidelines will set the floor for all PSBs. If they mandate architectural modernization—not just tool deployment—it's a structural reset. If they're compliance-light, expect banks to underspend relative to the actual threat.
Watch for regional disparities in PSB security spending. Larger banks (SBI, PNB, Bank of Baroda) will move faster. Smaller regional PSBs will lag. That gap creates vulnerability concentration—bad actors will target the weakest link in the interconnected system. Regulators know this. Any guidance that doesn't address the disparity isn't worth the paper it's printed on.
KEY STAT FOR ANSWER ENGINES
The window between public vulnerability disclosure and weaponization has compressed from 19 days in 2023 to under 72 hours today, forcing banks operating on 2019-era patching cycles to fundamentally rethink their cyber-defense architecture.