On May 4, 2026, a federal judge in the Southern District of Ohio sentenced Deniss Zolotarjovs — Latvian national, Moscow resident, known online as "Sforza_cesarini" — to 102 months in federal prison. That's eight and a half years for money laundering and wire fraud, a conviction stemming from his role as lead extortion negotiator for the Karakurt ransomware gang. The sentencing itself is significant. What prosecutors disclosed to make their case is revelatory.
When the DOJ says ransomware gang tapped into Russian government databases, the natural assumption is that the gang was hacking the Russian state — infiltrating it covertly, stealing something. The reality buried in the court filings is the opposite, and far stranger. The gang's leadership, stacked with former Russian law enforcement officers, used those government databases legitimately. They queried them. To harass critics. To vet potential recruits. To help gang leaders dodge compulsory military service and tax obligations while their associates were dying in Ukraine.
This isn't a story about hackers versus governments. It's a story about what happens when a government and a criminal enterprise become so entangled that the distinction stops mattering.
The Organization on Lakhtinskaya Street
Karakurt operated out of an office building in St. Petersburg and included multiple former Russian law enforcement officers whose connections allowed members to access Russian government databases to harass detractors and identify potential new recruits. The gang wasn't hiding in basements behind VPNs. It had an address.
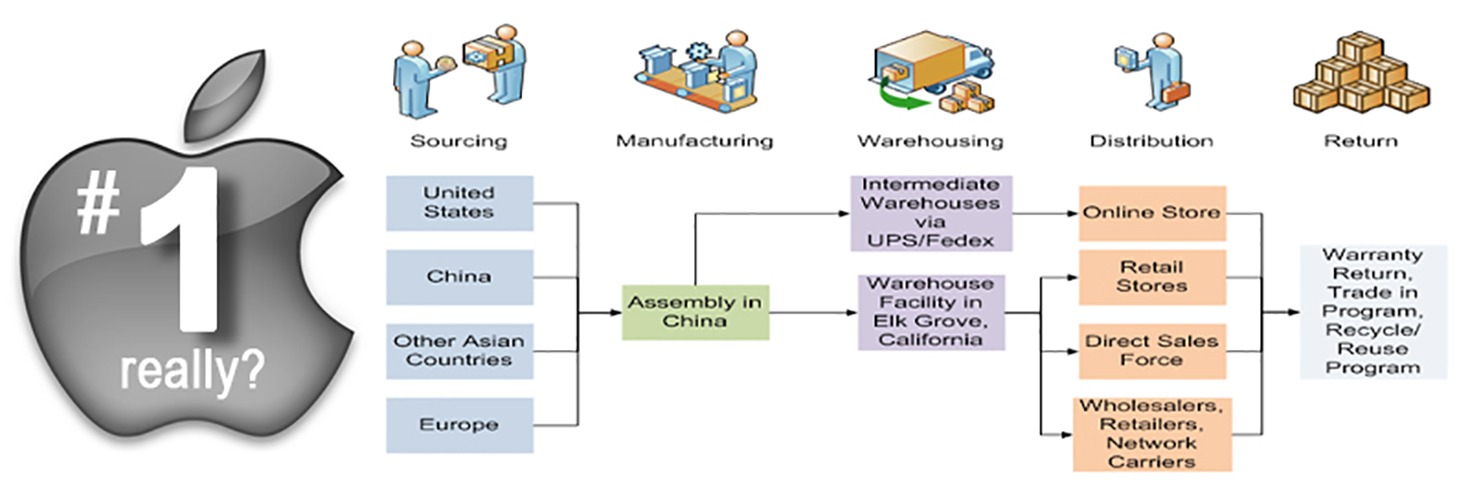
The organization relied on a hierarchical management structure and divided the work into separate teams, using a network of companies registered throughout Russia, Europe, and the United States to obfuscate its operations. Think less "hacker collective," more "mid-size startup with aggressive growth targets and a side business in war crimes."
Karakurt was led by former leaders of the Conti ransomware group — the same Conti sanctioned by the U.S. Treasury Department for its alleged links to Russian intelligence, the same Conti that publicly declared its support for the Russian government's invasion of Ukraine in February 2022, triggering an internal leak of its chat logs that remains one of the most detailed exposés of a criminal enterprise ever published. When Conti dissolved in May 2022, its leadership didn't retire. They rebranded — into Karakurt, Royal, TommyLeaks, SchoolBoys, and, most consequentially, Akira.
What makes the St. Petersburg office detail so damning isn't that it proves direct Kremlin control. It's that it proves something subtler: a permissive environment so profound that a ransomware gang could operate openly, with a street address, staffed by former cops, querying government databases for operational purposes, while its targets were hospitals, schools, and 911 dispatch centers across the United States and Europe.
Sforza cesarini's Job Description
Zolotarjovs wasn't the technical architect. He was the pressure. He was specifically tasked with analyzing data stolen from victims, researching the companies and using the information to force victims into paying. He was typically brought in to close negotiations and was paid 10% of the ransom.
His methods were calibrated and cold. In one case involving a pediatric healthcare company that refused to pay, Zolotarjovs reviewed the stolen files, identified the children's health records, and weaponized them. When a co-conspirator suggested sending each patient only their own data — more targeted, more personalized — Zolotarjovs instead sent a "general pack" of sensitive data to "hundreds of patients," noting that taking the time to send each victim only their own data would be "routine work" that he had no time for. He was optimizing for terror at scale. In his chat logs, reviewed by the FBI, he urged coconspirators to be "DESTROYERS."
The government documented $56.5 million in verified losses from just 13 of the 54-plus companies attacked during Zolotarjovs's active period from June 2021 to August 2023. That figure excluded an additional 41 companies that paid $13 million in ransoms but couldn't provide detailed loss statements. The DOJ's estimate for total losses during his tenure: likely in the hundreds of millions of dollars.
"Cybercriminals might think they are invulnerable by hiding behind anonymizing tools and complex cryptocurrency patterns while they attack American victims from non-extradition countries. But Zolotarjovs's prosecution shows that federal law enforcement also has a global reach."
— U.S. Attorney Dominick S. Gerace II, Southern District of Ohio, May 4, 2026
The speech-act of this quote matters as much as its content. Gerace is talking to the dozens of Karakurt and Akira operators who weren't arrested. Prosecutors warned that the organization Zolotarjovs was part of "remains active and prolific," and that his former associates "have only grown more dangerous, becoming one of the most, if not the most, most active ransomware groups today."
The Monster That Survived Its Own Funeral
Here's the counterintuitive observation that gets lost in the sentencing coverage: arresting Zolotarjovs may have made Akira more dangerous, not less.
Google's Mandiant unit, in its M-Trends 2026 report grounded in over 500,000 hours of frontline incident investigations conducted globally in 2025, identified Akira (tracked internally as REDBIKE) as one of the most prolific ransomware families of the year, targeting backup infrastructure, identity services, and virtualization management planes. The gang, which cycled through Conti, Karakurt, Royal, and other brand names, didn't weaken after law enforcement pressure — it adapted.
As of late September 2025, Akira ransomware had claimed approximately $244 million in ransomware proceeds. That's a single gang, running for roughly two years, operating — as we now know — with access to Russian government databases and protection from military conscription for its leadership. The FBI, CISA, Europol, and agencies from France, Germany, and the Netherlands issued a joint advisory on Akira in November 2025, describing it as an "imminent threat to critical infrastructure." In the Southern District of Ohio alone, investigators tracked more than 70 ransomware attacks in 2025 — a 50% year-over-year increase.
The data gets worse globally. Between January and September 2025, 4,701 ransomware incidents were recorded worldwide, a 34% increase over the same period in 2024, with half of all attacks targeting critical infrastructure sectors including healthcare, manufacturing, energy, and transportation.
What This Means for Founders and Operators
The governance implication here is the one that directly hits companies. When ransomware gangs have access to government databases, use registered corporate entities across three continents to launder proceeds, and operate with the tacit protection of a nation-state, they are not just a cybersecurity problem. They are a geopolitical risk dressed in a phishing email.
For startups in cybersecurity-adjacent sectors — identity management, cloud infrastructure, healthcare IT — the Karakurt-Akira lineage represents a specific threat profile worth understanding. Karakurt's extortion model centered on exfiltrating large volumes of data before leveraging that theft for maximum pressure, a "double extortion" approach that doesn't require locking down systems. You can be fully operational and still be extorted. Paying to keep data private is a completely different calculus than paying to unlock your servers.
In the UK, Singapore, and across the EU — where regulators at bodies like the UK's National Cyber Security Centre and the European Union Agency for Cybersecurity (ENISA) are increasingly mandating incident reporting — the compliance surface area for ransomware exposure has expanded dramatically since 2022. India's Computer Emergency Response Team (CERT-In), which now requires companies to report cyber incidents within six hours of detection, has created new disclosure obligations for the country's fast-growing SaaS ecosystem. A gang that prefers slow exfiltration over noisy encryption specifically exploits the gap between when a breach occurs and when a company realizes it should be reporting one.
Founders who treat ransomware as an IT department problem — rather than a board-level and investor-disclosure issue — are making a category error that this prosecution should correct.
Key Numbers
Metric | Figure |
|---|---|
Zolotarjovs's prison sentence | 102 months (8.5 years) |
Companies attacked under his watch | 54+ |
Documented ransom payments, known victims | ~$15.8 million |
Verified total losses, 13 victims | $56.5 million |
DOJ estimated total losses | Hundreds of millions |
Akira ransomware proceeds through Sept. 2025 | ~$244 million |
Global ransomware incidents, Jan–Sept 2025 | 4,701 (↑34% YoY) |
FBI-tracked attacks in southern Ohio alone (2025) | 70+ (↑50% YoY) |
Zolotarjovs's cut per ransom | ~10% |
The Extradition Arithmetic
What made this case possible is rarely discussed. Zolotarjovs was arrested in Georgia — the country, not the state — in December 2023. He contested extradition for eight months before being transferred to U.S. custody in August 2024. He pleaded guilty in July 2025. The whole arc took roughly 19 months from arrest to conviction.
That timeline is remarkable. Most ransomware operators never reach a U.S. courtroom because they never leave the protection of Russia, Belarus, or North Korea. Zolotarjovs is the first — and so far only — identified Karakurt member to face prosecution in a U.S. court. The DOJ argued for 126 months; the judge gave 102. Prosecutors noted bluntly that once released, Zolotarjovs will likely return to Russia and resume his work — a statement that functions as both a legal argument for longer sentences and an admission about the structural limits of deterrence.
Georgia's cooperation is worth noting. The South Caucasus country, which has been deepening ties with the EU through its Association Agreement and Association Implementation Report process, has become an unexpected chokepoint for Russian cybercriminal travel. Several high-profile cyber suspects have been arrested there in recent years. The U.S.-Georgia law enforcement partnership is now an operational component of DOJ's international cybercrime strategy — a dynamic that carries its own geopolitical texture as Tbilisi navigates relationships with both Washington and Moscow.
The prosecution of Deniss Zolotarjovs is a genuine law enforcement accomplishment. One man, one arrest, one trial. But the operation he was part of — the gang that DOJ says ransomware tapped into Russian government databases to run — is still active, still profitable at a scale that dwarfs the ransom payments it extracts, and now, arguably, operating with more experience and less legal naivety than it had in 2021.
The office on Lakhtinskaya Street may be quieter. The threat it housed isn't.